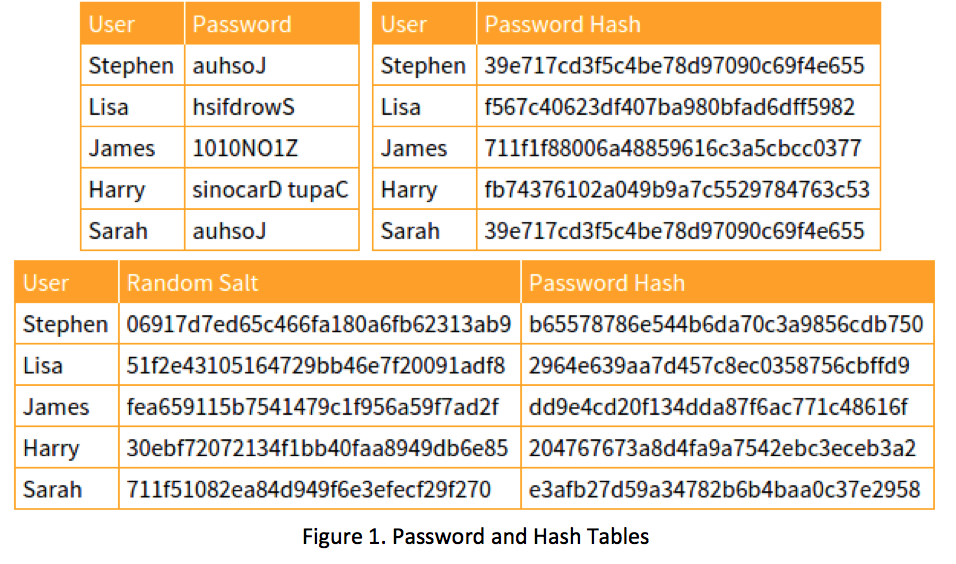
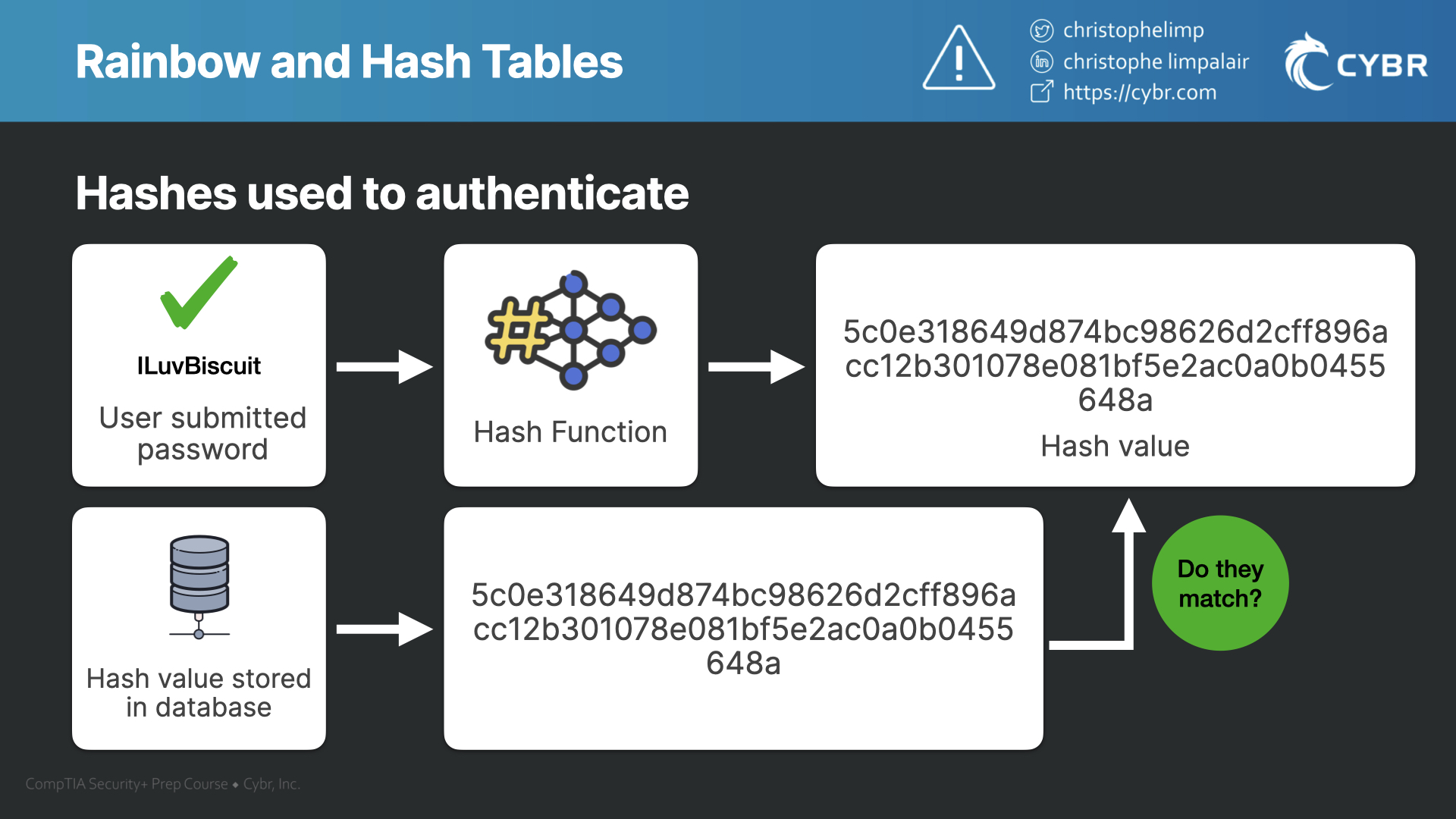
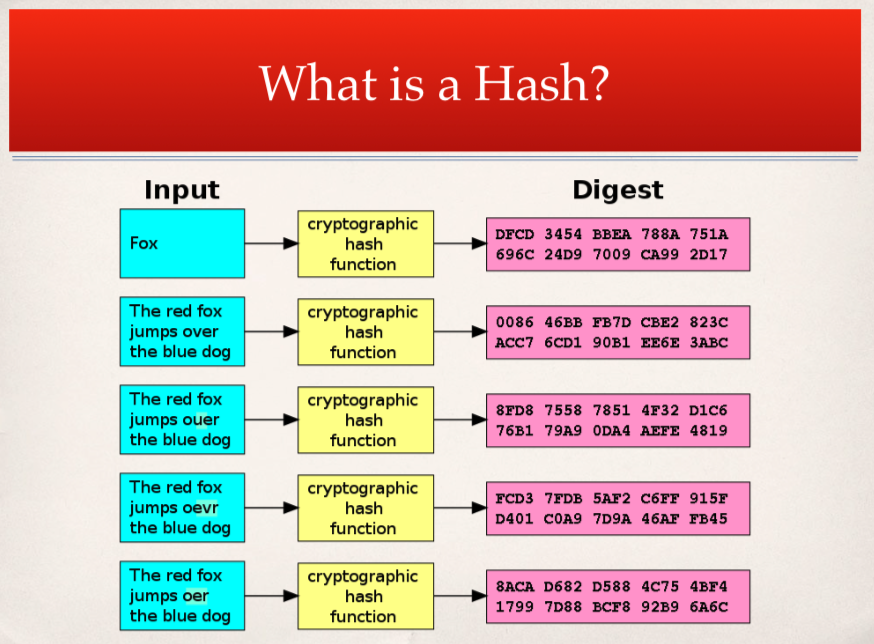
KALI – How to crack passwords using Hashcat – The Visual Guide | University of South Wales: Cyber University of the year: Four years running: 2019, 2020, 2021, 2022
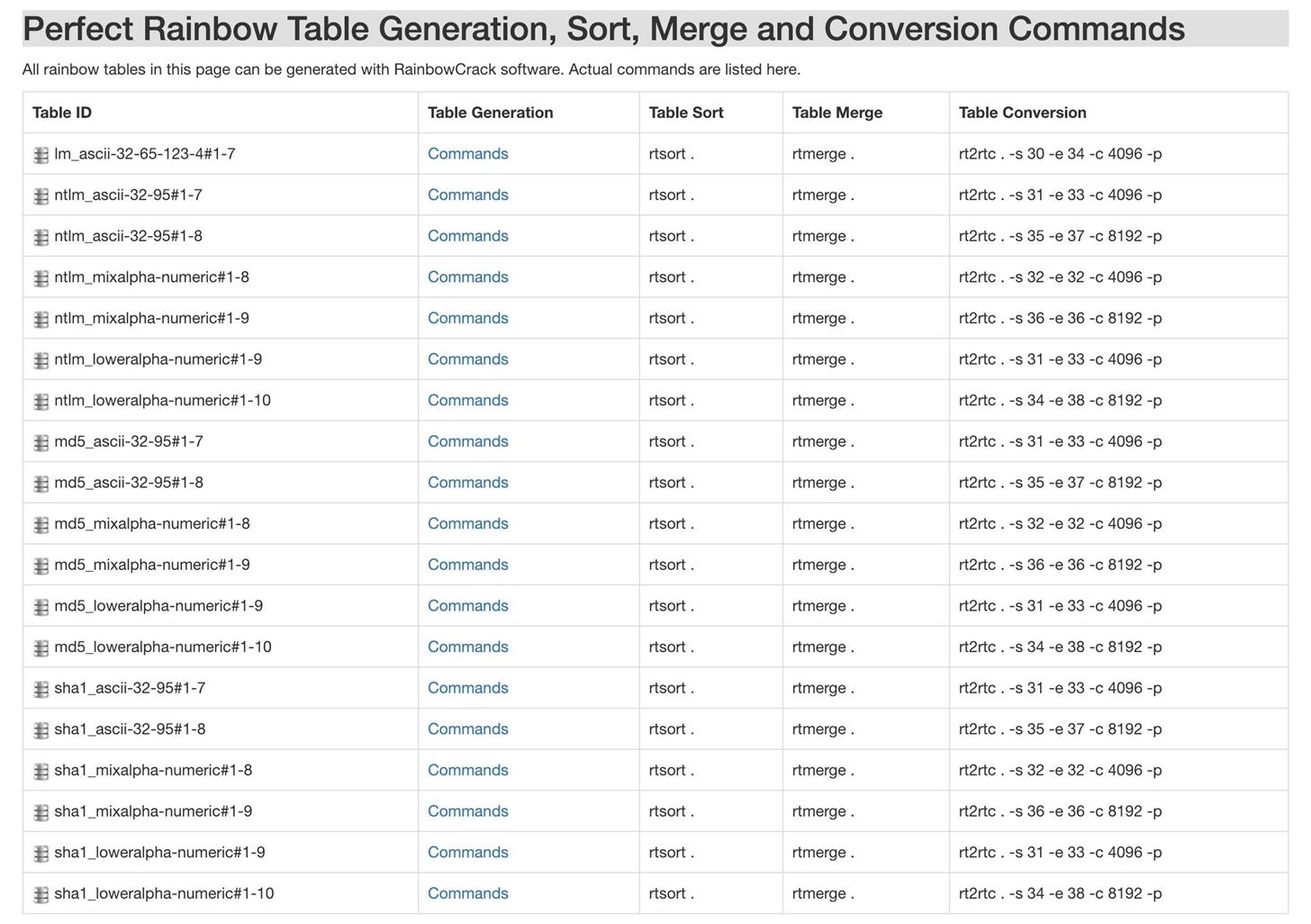
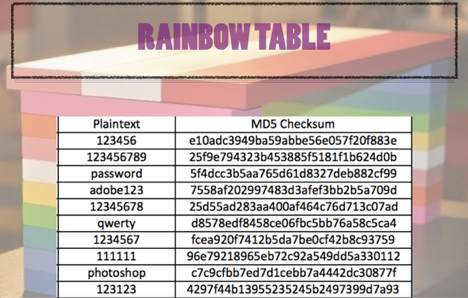
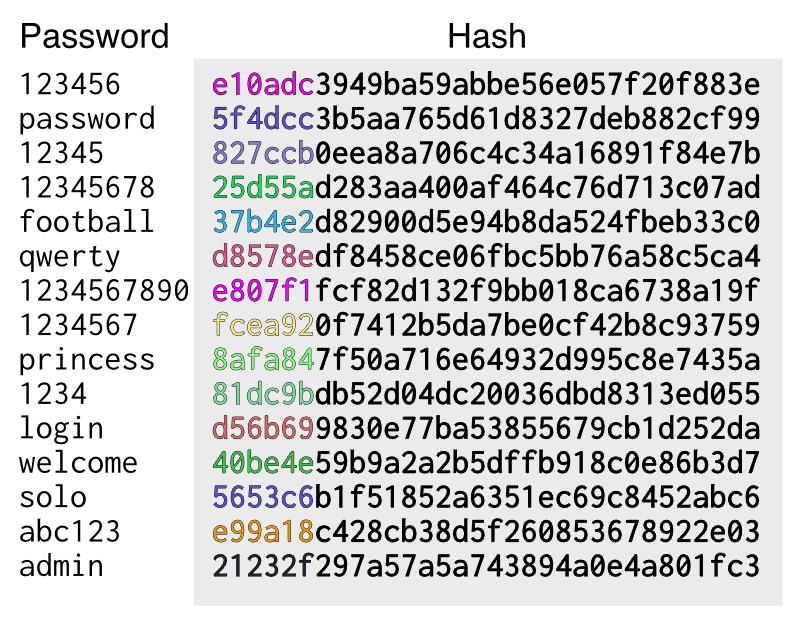
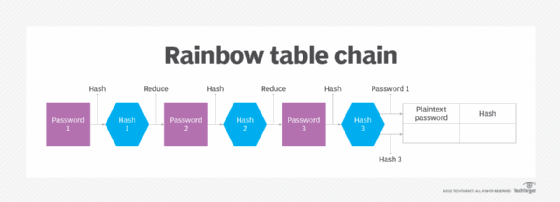
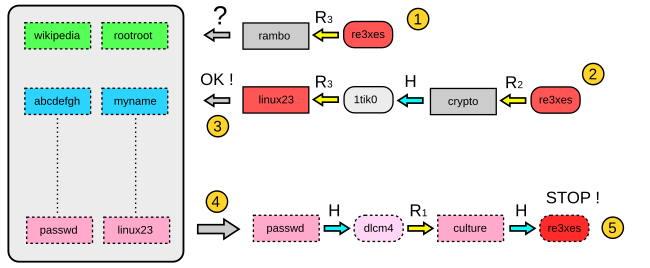
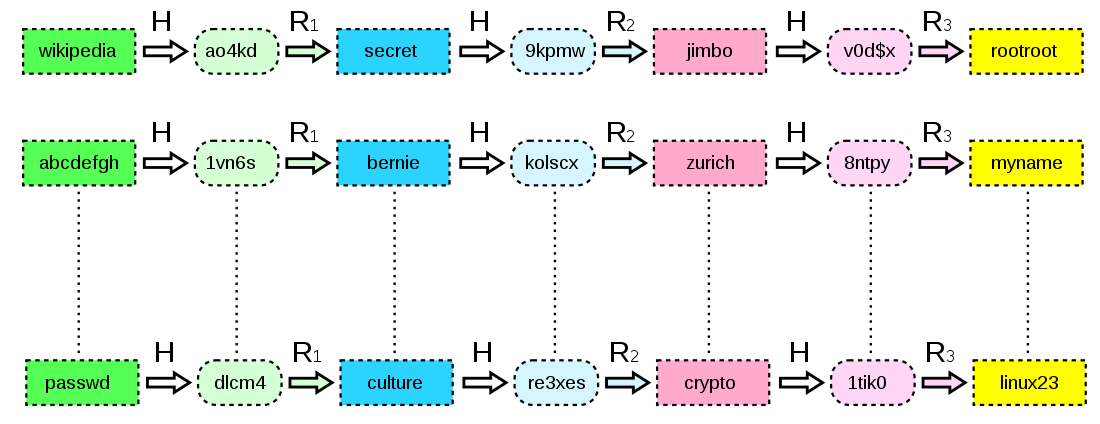
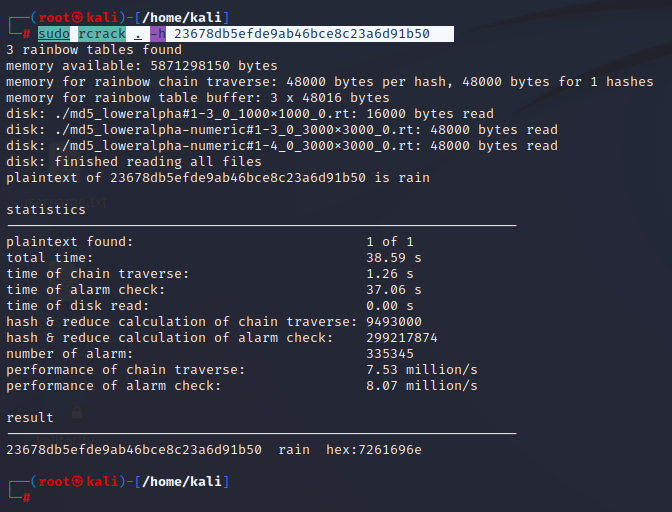
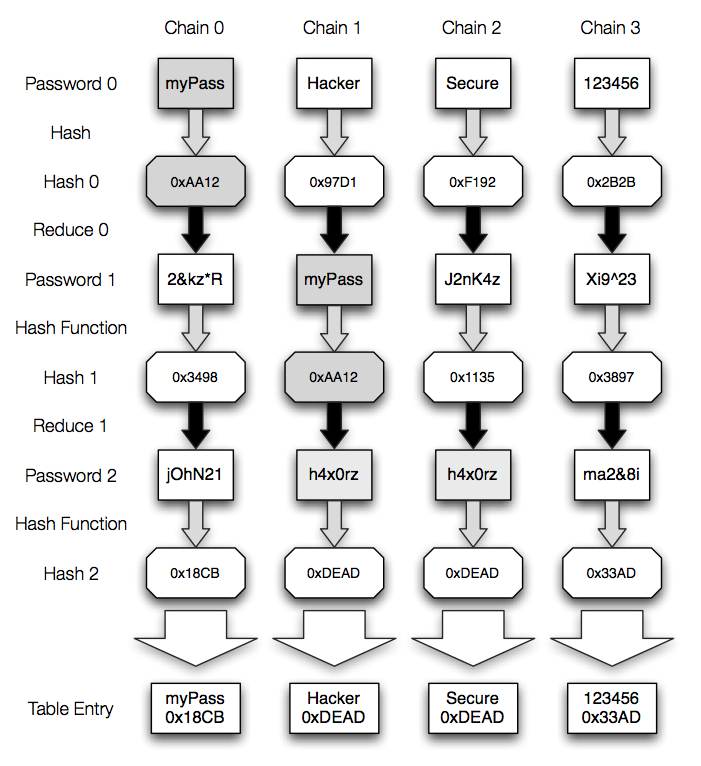
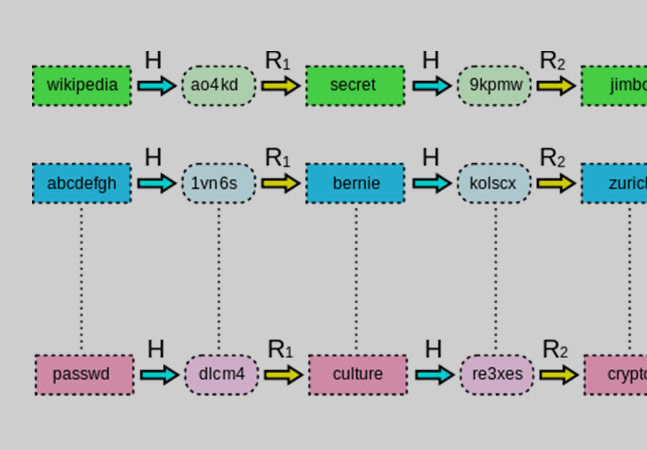
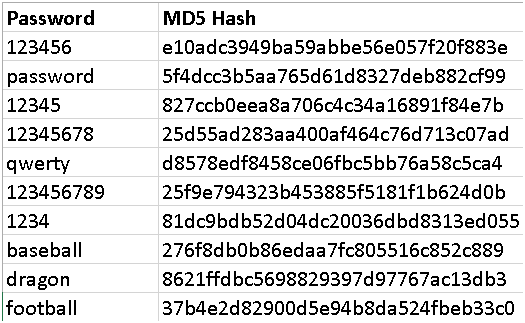
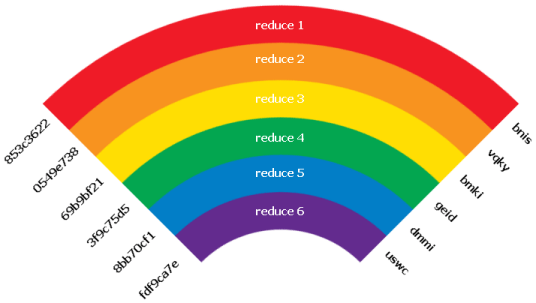
How to Create Rainbow Tables for Hashing Algorithms Like MD5, SHA1 & NTLM « Null Byte :: WonderHowTo